So you have installed a new image on your VirtualBox, Congratulations, its actually a great tool. Now, you will always be facing the same error – always for the same reason – Vbox client is not set, and thus the clipboard bidirectional use is not working. Once the settings in VirtualBox is set, and bidirectional […]
Latest feeds
Integrating Syft and Grype into CI/CD Wo...
In today’s fast-paced software development environment, security must be a first-class citizen in every phase of the deployment process. By integrating security scanning tools such as Syft and Grype into your CI/CD workflows, you can catch vulnerabilities early—well before your code reaches production. This article will guide you through the benefits of these tools and […]
Structuring Your Terraform Codebase for ...
As a DevOps consultant, I’m often brought into companies to advise on the best way to structure their Terraform codebase. While there isn’t a one-size-fits-all approach—since every organization has unique requirements—I’ve developed a structure that works well for most, if not all, companies. In this article, I’ll outline this structure and explain why it’s an […]
The Rise of On-Demand AI Insights and th...
Introduction Over the past few years, I’ve immersed myself in the world of data—collecting, cleaning, analyzing, and most importantly, visualizing. Like many professionals, I relied heavily on dashboards to bring data stories to life. Yet as I delved deeper into user needs, I realized a key challenge: the more dashboards I built, the harder it […]
General tips for communication with your...
Whether you’re collaborating with colleagues or chatting with friends, optimizing your conversations can save time and improve productivity. To help you achieve this, here are five essential rules for efficient digital communication
GA4 attribution models
Understanding GA4 Attribution Models through Creative Visualization
Unlock the secrets of user conversion paths with our illustrated guide to Google Analytics 4 Attribution Models. Discover how each model attributes conversion value, enhancing your digital marketing strategy.
First Click Attribution Model: Unravel the j
Exclude audiences from all campaigns Goo...
Google ads platform allows you to use scripts, here are some of my favorites, when it comes to excluding career page viewers, returning customers
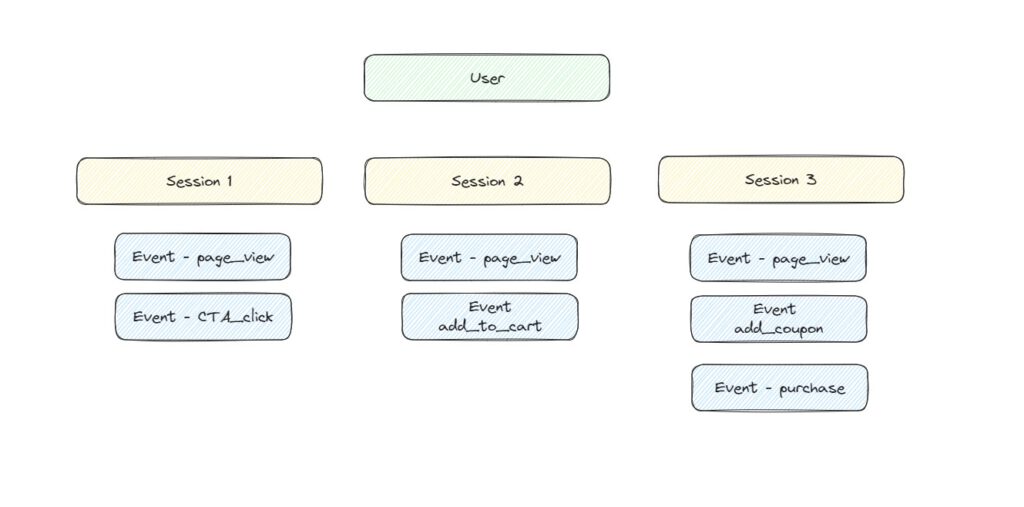
GA4 source explained
The first part of understanding the three types of sources is understanding the structure and relationship between the user, session, and event. In the following drawing, we can see the structure of user–>session[s]–>event[s] The source type filtering that can be found in GA4 is divided into 3 main types:1. First user source: self-explanatory.2. Session source: […]