1. The articles contained on the website are for educational purposes only encouraging users and Admins to better understand the environmental security measurement and enable safer digital environment.
Geek-KB.com does not encourage, condone, or orchestrate attempts of hacking into other servers or any other illegal activities. All actions taken by users are strictly independent of Geek-KB.com. We are not responsible for any misuse of the techniques listed on this website.
2. Geek-KB.com has the sole discretion to remove/edit users, articles, external resources, or any other user-submitted content to protect itself from legal harm. This legal disclaimer may be modified at any time without notice.
3. Any damage caused by using any of the techniques taken from https://www.geek-kb.com is at your own risk and responsibility;
Table of Contents
In this Generate Rainbow Tables Using WinRTGen tutorial:
Rainbow tables are usually used to crack many types of hash such as NTLM, MD5, SHA1, etc…
This tool will help us to create a large dictionary file which will later be used to crack many hash types such as the ones stated above.
I used these tables to crack some passwords on my lab using rcrack.
System Requirements:
A Windows 7 or later machine.
Let’s begin:
One thing you must remember, you must be aware to the large hard disk consumption that the tool generated.
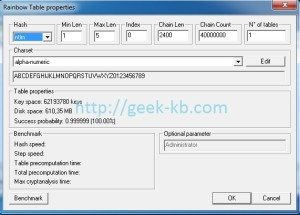
For this tutorial I’ll create simple rainbow table for 1 – 5 alphanumeric, and it costs about 613MB of your hard disk space
If you intend to create a huge dictionary which contains alphanumeric, space, characters, Take into consideration that the table may reach size of 5gb.
There are many ways for generating rainbow tables, b
and so, geek-kb is proud to present:
How To: Generate Rainbow Tables Using WinRTGen
Hash types – The type of hash you’re going to generate tables for.
lm: classic LanManager hash. Limited by its nature to 7 uppercase chars (you can generate tables for lowercase or 8 or more chars passwords, but it’s a waste of time). Tables are compatible with rcrack
fastlm: LanManager hash. Same as lm but optimized for MMX instruction; It’s faster than “lm” in both in generation and cryptanalysis on P4 Centrino (or superior) processors. Not compatible with rcrack.
ntlm: NTLanManager hash. A newer hash for M$ authentication, and the only one you’ll find in the belly of a PC that has some serious security setup. Password are not converted in 7 uppercase chars chunks.
lmchall: used to attack the sniffed (not dumped!) LM authentication as a whole. Requires the challenge to be poisoned to a corresponding value.
Unconvenient: better to use halflmchall and go brute with the remaining chars.
halflmchall: used to attack the first 7 chars of a sniffed (not dumped!) LM authentication. Requires the challenge to be poisoned to a corresponding value. Using halflmchall + brute is always better than pure lmchall.
ntlmchall: used to attack the sniffed (not dumped!) ntlm authentication. Requires the challenge to be poisoned to a corresponding value. Similar to lmchall, but there can be no “halfntlmchall” so you get to go with it.
mscache: used to attack the cached credentials of the previously logged users. Requires each tableset to be generated for a specific username. The proposed value: “Administrator” is possibly the most interesting in many cases.
md2: md2 hashes
md4: md4 hashes
md5: md5 hashes.
sha1: sha-1 hashes.
ripmed160: ripmed160 hashes
mysql323: mysql323 hashes
mysqlsha1: mysqlsha1 hashes
ciscopix: cisco pix firewall hashes
sha256: sha256 hashes
sha384: sha384 hashes
sha512: sha512 hashes
oracle: oracle hashes – Requires each tableset to be generated for a specific user name.
wpa-psk: wpa-psk hashes. Requires each tableset to be generated for a specific ESSID. Unlike Oracle not all wlans use the proposed ESSID (“wlan”) as default.
Min len / Max len: The minimun and maximum length of the included passwords. This is the first of the two parameters that define the keyspace. Note that raising the min value usually lowers the keyspace by a negligible amount.
Index: The tables discriminator. It Is very important to understand this: the table index and _not_ the file number gives you the identity of a table. Multiple files sharing the same index pertain to the same table.
Chain len (or “t” parameter): The number of hashes represented by a single chain. A chain always uses the space of two hashes (the first and the last) on disk. This is one of the parameters that define the keyspace coverage.
*** As a rule of thumb, the longer the chains the higher the success rate but also the per-hash cryptanalysis time of the interested table. ***
Chain count (or “m”/”N°of tables”): The number of chains in a file. This is one of the parameters which define the keyspace coverage.
*** As a rule of thumb, the more the chains the higner the keyspace coverage, but also the disk usage and so the disk-access time. ***
Too much (and too long, see previous point) chains in a single table produce merging chains and wastes.
N° of tables: A misleading title. Should be: “N° of files for current table index”. It’s a mere extension of the chain count: since you must keep file each file below the 2Gigs barrier you’re given the chance of creating more files. Note that the success rate displayed by winrtgen refers to DIFFERENT TABLES, not more files with the same index
Charset: defines what characters will be used in the randomly-chosen plaintext to hash (ok, the passwords ). This is the second of the two parameters which define the keyspace.
You can edit the file manually or by clicking on the “edit” button.
The file is also used for charset selection by the bruteforcing engine.
1. Download WinRTGen below
| Mediafire.com |
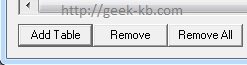
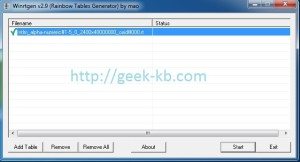
2. Run WinRTGen, and then click Add Table
3. In the Rainbow table properties:
you can see an example to create a ntlm table made of 1-5 characters, the index starts from 0, so if I set the N^ of tables value to 5, the index will rename the file into index 0,1,2,3,4(5 tables)
4. When you finish setting up all of the properties, just click OK, and in the main program click OK once again to start build the tables. You can leave your computer and go out or something because it’s a very long process.
It took about 6 hours to complete the process.
Have fun and feel free to leave comments!



No Comments Yet